Even with the invention of social media platforms, instant messaging, and video calling, most of us still depend heavily on emails. It’s such a convenient way to send messages and files to a friend, family member, or colleague.
Unfortunately, emails are unbelievably insecure. I’m sure that most Americans have heard about governmental surveillance programs that were brought to light by Edward Snowden, such as the PRISM program. PRISM (among other wiretapping endeavors) was created to mine vast amounts of domestic communications, and emails are no exception.
Google’s services were heavily influenced by the federal government, and the NSA wrote a lot of back-door modules into Google’s services to mine data. But Google is only one of many services that complied with the PRISM program. Other domestic US firms that were forced to comply include Microsoft, Apple, Yahoo!, and other similar tech firms.
The bottom line is that we don’t know how many email services the NSA has invaded, because things are always changing at an ever-increasing rate.
Even though Snowden released documents detailing the activities of the NSA, they could have very well invaded even more email services today. That frightening thought leaves many Americans (and other nationalities) feeling as though their right to privacy has been infringed upon.
The good news is that there are simple measures you can take to encrypt your emails (and related content) to ensure that hackers, thieves, disgruntled employees, and federal authorities don’t have the ability to snoop through your email data. However, I first wanted to let you know about temporary email accounts.
Common Email Alternatives and Temporary Accounts for Anonymity
Before we dig into the nitty-gritty details of encryption and its nuances, I wanted to bring one point to your attention. Sometimes, it may be preferable to use an anonymous email service. One of the problems with services like Gmail and comparable alternatives is that they are linked with other accounts.
For instance, Outlook.com accounts are frequently tied to individual Microsoft systems, and Gmail addresses are often connected with other Google services, such as Google Drive. As such, these services can build an accurate collection of information that easily identifies you. If you want to sign up for a service or send an email anonymously, I’d recommend using a free and disposable email address service.
Services like Mailinator, Mailnesia, and TempInbox will provide you with a temporary email address that is nigh on impossible to trace back to you. However, I wouldn’t recommend using a temporary email address to send mission-critical or sensitive emails.
Understanding Email Encryption
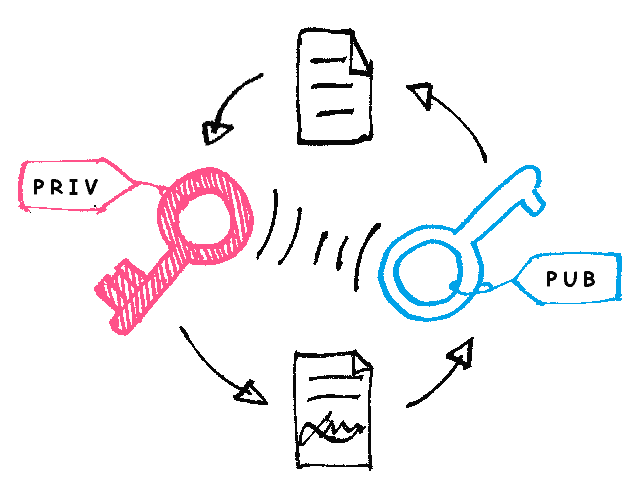
For complete email protection, there are 3 essential things that should be secured with encryption. Firstly, the connection to the email server needs to be encrypted to prevent eavesdroppers from capturing email data as it traverses the public Internet.
Secondly, the content of emails that you are sending needs to be encrypted as well. Thirdly, the last thing that needs to be encrypted is archived email data. As far as the first requirement is concerned, you’ll find that any modern and popular service that uses a web portal is going to secure the connection using HTTPS.
Note that when using Gmail in a web browser, the padlock icon, as well as the beginning of the URL both, indicate the use of HTTPS.
But Gmail and other similar services don’t always encrypt email content default. A fair few do include encryption features, but by and large, you’ll likely need to turn to third-party tools to ensure that your emails are properly encrypted.
How to Encrypt the Content of Your Emails
If you want to send an encrypted email to another individual, it’s going to require you both to make some configuration changes before you can send secure emails. Perhaps one of the easiest and simplest ways to encrypt emails is to use third-party browser extensions. The one that you select is largely based on who your email provider is and which browser you are running.
Using Gmail as an example (because it’s so widely used), I would recommend using SecureGmail. You can easily secure an email with a password used to secure the content with an encryption algorithm. However, make certain that you don’t send the recipient of the email the decryption password in plain text. Doing so would prevent the whole point of using email encryption.
And though it includes wonderful encryption and decryption mechanisms, there are a few stipulations to using this tool. For example, the receiver of the email must also be using Gmail, they must know the decryption password, and they also have to have SecurGmail installed. Nevertheless, SecureGmail isn’t the only email encryption service – far from it. They are a dime a dozen, though SecureGmail is one of my favorites for Gmail.
Users with other email providers may have to hunt around for the right tool in their browser’s add-on database. However, Virtru is another great alternative for users of Firefox. They do have paid versions of their email encryption service that come jam-packed with extra security features. But there’s also a free version for personal use that will help encrypt email on your local computer before sending it.
It’s also worth noting that email archives need to be encrypted as well. Again, this depends on the environment you’re in, and what email service you’re using. For instance, if you’re in a corporate or medium-sized business setting, it’s likely that you have your own email servers. Just think of all the damage an attacker could do if they were able to access the email archives and backups on the server. You’d have a political-grade email scandal on your hands.
Most email services and front-ends, such as Gmail or Microsoft Outlook, have ways to create backup archives of your data. If you don’t see an option in your specific interface, you can always use a third-party file encryption service to lock down the archive backups.
Encrypting Local Email Files on a PC
Web interfaces aren’t the only way to access emails, and some people like to use email clients that run on their local machines, such as Outlook and Thunderbird. If you’re the type of person that uses a program or application on a local device instead of using a web browser to access mail, one virus could send all of your private emails into the hands of a hacker.
And there are a lot of different solutions to mitigate these types of attacks. First of all, it’s best to use a drive encryption service. For example, Windows 10 has a feature that fully encrypts your hard drive.
Furthermore, it’s better to set a BIOS password so a hacker can’t change the boot order in your BIOS to boot to USB, and then use a live boot thumbstick (like Ubuntu Live) to access the hard drive.
Most mobile devices include a storage encryption feature, too. Most email clients will include some sort of local encryption feature, though that varies a lot among different email clients. If your client doesn’t have such a feature, you can easily use a free utility like TrueCrypt or VeraCrypt to encrypt the actual email data files on your computer.
However, it’s a nuanced process, because you’ll have to do a bit of homework to find out where in the file system your particular email client stores its data.
Workarounds
There are also plenty of workarounds for those of you who want to send and encrypted email, but you’ll find that they are rather clumsy, inconvenient, and aren’t elegant solutions. If you’re really in a bind and need to send encrypted textual content to another individual, you can always send them an encrypted text file.
If the person you are trying to reach doesn’t have the same email provider, browser add-on, or for some reason can’t access the right tools to send encrypted email, you can email an encrypted text file as an attachment. Then, once the receiver downloads the text file, they can decrypt it on their local computer to read your message.
Just make sure they know the encryption key beforehand, and make sure that you don’t send it in an unencrypted format. Though the risk may seem low, emailing an encryption or decryption password in plain text is poor practice – especially if you send it in the same email in which you attached the encrypted file.
This isn’t really the most practical or ideal solution, but like I said, it serves the purpose of sending encrypted text to another individual.
Final Thoughts
Most of the standard email protocols like IMAP (Internet Message Access Protocol) and POP (Post Office Protocol) don’t include their own encryption mechanisms. That makes it necessary to encrypt emails using third party tools that function in the application level of the OSI model. Otherwise, raw email data can be intercepted as it is sent from one mail server to another, or from a mail server to a client.
In summary, I’d recommend the following tools as the top two for sending encrypted emails for the average user:
However, there are a lot of different email encryption tools, addons, extensions, and third-party services such as the following:
- Comodo’s free secure email certificate using S/MIME
- HushMail
- Rmail
- Sendinc
I really think that SecureGmail and Virtu will fit most people’s needs and help you send encrypted emails. But there’s a lot more to email data security than meets the eye. Remember to only use trusted mail servers, and to encrypt your local data so it isn’t stolen by a hacker!