- Canopy vs Bark Compared: Which is Better for Families? - September 21, 2023
SSL (Secure Sockets Layer) is an integral part of the Internet, and it’s used to create a secure, encrypted tunnel between to remote endpoints – which are usually a web browser and web server. Sometimes, however, it is used between different endpoints, such as a mail server and a mail client.
SSL helps keep personal information like usernames and passwords, payment card data, and social security numbers out of the reach of hackers and eavesdroppers through encryption.
Usually, when data is sent between devices over the public Internet, it isn’t encrypted or secured by default. If a hacker gets their hands on data in transit through the public Internet before it has been encrypted, they can easily read it and steal your data.
SSL is a protocol specifically designed for security, but the protocol can be a little difficult to understand if you don’t come from a technical background. Consider that SSL is extremely popular, and each day it secures millions and millions of people’s data around the globe. Whenever you’re using an HTTPS or SSL connection, you’ll see a small padlock icon in your browser that indicates your connection is secure.
What Are SSL Certificates?
SSL certificates are composed of two primary parts: a public key and a private key. These keys operate together to provide encryption for any given SSL connection. In addition, the certificate also holds a piece of information known as the subject, which is really just a fancy way of describing the identity of the computing system or server that owns the certificate.
There are essentially two ways to obtain an SSL certificate: You can either self-sign your own or purchase one and create a CSR (Certificate Signing Request) on your server
Doing so sets up the private and public keys on your web server, and creates a CSR file that you’ll have to send to the issuer of the certificate (which is sometimes referred to as the Certificate Authority). In turn, the CA will use the CSR file as input to create a private key without ever seeing it.
The algorithm was designed in such an intelligent way that the CA can generate your private key without compromising it and seeing its value. Once you get your SSL certificate in your hot little hands, it’s time to install it on your web server. In addition, people typically install an intermediary certificate before they install the root certificate.
By now you might be wondering why you should go through the trouble of buying an SSL certificate if you can just sign one on your own, the answer boils down to trust and credibility.
When I connect to a website and see that it has been secured with a certificate from a trustworthy organization (like DigiCert), I don’t think twice about establishing a connection with that server.
On the other hand, if I were to see a certificate signed by Joe-Shmoe, I wouldn’t make the connection. Joe could be hosting a shady web server in his mother’s basement for all I know, and the connection could be dangerous.
One of the most important qualities of an SSL certificate is the fact that it was signed by a well-known and respectable organization.
Anyone and their dog can make a certificate, but browsers won’t automatically make connections with SSL unless the certificate is on a pre-made list of trusted Certificate Authorities.
If the certificate doesn’t come from a trusted CA, most browsers spit out some type of warning, saying that the connection could be dangerous. The user then has to manually opt for the shady certificate before making a connection.
And it’s not as easy as you might think to get on the list of trusted CA’s. Before an organization can become a member of the CA list, they have to meet numerous compliance standards and be audited by a third-party security organization.
Having a certificate signed by a CA means that the organization’s identity has been verified. This quality helps mitigate phishing attempts on the Internet. Because your browser can trust the connection with a trustworthy CA-signed certificate, it can then trust that the website it’s connecting to is legitimate.
Creating the Secure Connection
The process of setting up an SSL certificate is actually pretty complex, but we’re going to boil it down a bit. Whenever a user tries to connect to a website that uses an SSL certificate, the server, and the browser first perform what’s known as an SSL handshake. The handshaking process happens in the background, and the end-user can’t see this process in action unless they use a packet capture program on their local network interface.
During the handshake, three components of the SSL certificate are used, including the public key, private key, and session key data. Any data that has been encrypted with the public key cannot be decrypted unless the remote system has the private key.
However, the public and private keys are only used to setup the secure tunnel. Encrypting data with the public and private key can eat up a lot of local computing resources like memory and CPU cycles, so after the secure tunnel has been created, the session key is used to encrypt data exchanges and payloads.
Why You Need SSL
Just about every respectable website should be using SSL, and I’ll tell you why. We live in the information age, and one security breach, no matter how small, could mean the difference between living with peace of mind and having your identity stolen.
The average computer user is becoming smarter and more sophisticated, and people care more about Internet security (generally speaking) than they did even a few short years ago.
Every week there’s some new headline regarding how a hacker made off with hundreds or thousands of usernames and passwords, credit card numbers, or other similar types of personal information.
And believe it or not, Google uses HTTPS as a ranking factor when determining which websites show up at the top of search engine results pages. If your website gathers any kind of personal information from your customers (like address, name, payment card data, etc.), you need to lock that information down with an SSL tunnel.
Otherwise, you’re putting your visitors in harm’s way. Some of you may be thinking that since your site doesn’t engage in payment transactions or exchanges of personal information, that you don’t need SSL. But I disagree – I think SSL still holds a lot of value.
“Apart from providing raw encryption and security, it also adds a trust factor.”
Trust is key for any website; without it, users may fall victim to a phishing attempt.
Keeping that in mind, let’s take a look at the top 5 best SSL certificates for webmasters.
#1 Comodo
Comodo is based out of New Jersey, and they’ve also created other security products, such as a free software firewall solution. They are an international brand and are one of the biggest names in the SSL industry.
They own roughly a third of the market, and their SSL packages have great features and benefits like 2048-bit signatures for stronger security, 256-bit encryption, and browser recognition.
They are a good option for small businesses because their pricing is extremely competitive. Typically the SSL certificates start at $76.95, but they’ve run promotions in the past that make the price as low as $29.95 here. They are safe, trusted, secure, and inexpensive. What’s not to love?
#2 GeoTrust SSL
GeoTrust is the second-biggest name in the industry, and they have a smattering of different SSL options. They claim to have over 100,000 happy customers in over 150 countries around the world, and they can issue a certificate within a matter of minutes. Some of their top features include the dynamic date, 99% browser compatibility, 2048-bit signatures, 256-bit encryption, and unlimited server licenses.
They do cost more than Comodo, however, and a certificate with GeoTrust SSL starts at $149 here. They make it easy to secure your site with 1-3 licenses, and the longer your license term, the higher the discount.
#3 Symantec
Symantec is well-known in the computer world for their software and backup solutions. But this US-based firm also provides SSL certificates. Their certificate packages all include 256-bit encryption.
In addition, they have strong core features such as RSA certificates and DSA SSL certificates, Norton Secured Seal trust mark (which makes your site look even more safe, secure, and credible), daily malware scanning options, SAN support, and extra warranties.
But as the old saying goes, you get what you pay for. Symantec does a good job of providing feature-rich SSL services, but they are quite a bit more expensive than the previous two providers. Their certificate packages start at $399, though they do offer savings to people who choose longer-term subscriptions. With savings and discounts, customers can save as much as $200 here.
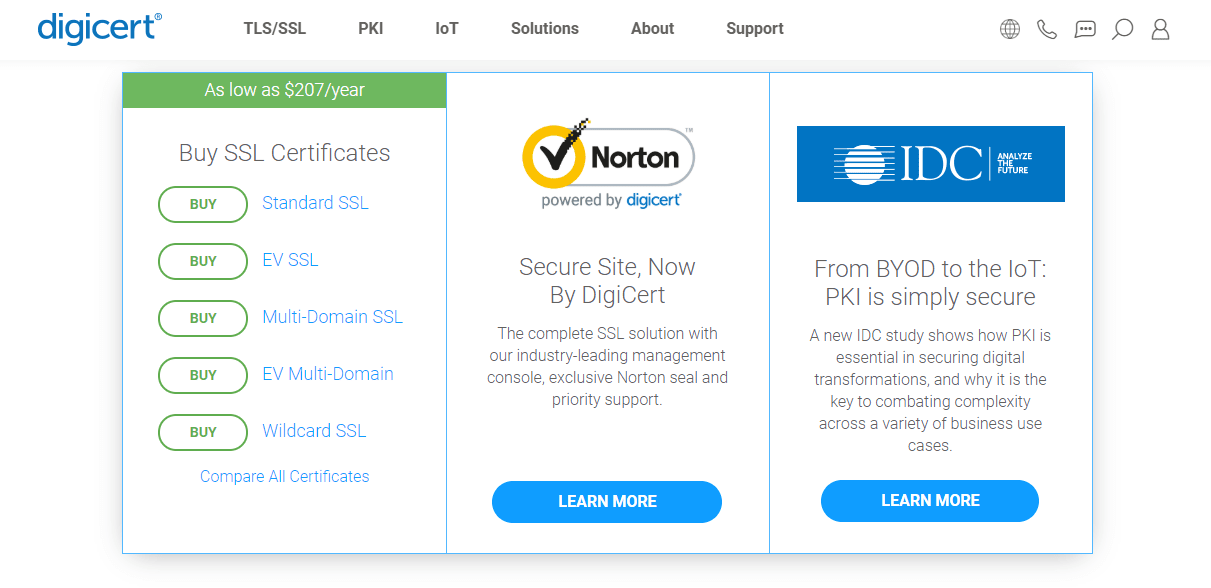
#4 DigiCert
DigiCert is another old and mature player in the SSL world. They are trustworthy enough to be used by some of the biggest businesses in the world, such as Amazon, Facebook, Yahoo, Microsoft, and many others. They, too, offer 2048-bit SSL signatures and 256-bit encryption. They don’t seem to have nearly as many security features as Symantec, which could be a good thing.
If you rely on other tools for security or have an in-house security team locking down your web servers, why pay extra for something you already have? DigiCert certificates can be purchased for as little as $156 per year here.
#5 GoDaddy
I had to include GoDaddy on the list for a couple of reasons. First of all, a lot of people go to GoDaddy for domains, so it makes sense that you could save time by getting your domain and SSL certificate in one stop.
Also, they’re one of the cheapest SSL providers I’ve seen, yet they’re still trustworthy. The cheapest certificates they offer are $69.99 here, but the Standard package is only $89.99. Depending on which package you choose, you’re roughly paying half of what the other providers charge.
Final Thoughts
If you want to make sure your users and website visitors are safe and secure, you really need to get an SSL certificate. Most businesses seek to establish long term relationships with their customers, and in order to maintain your relationship, you can’t mishandle their sensitive data or cause them to become the victim of a phishing attack.
Failing to care for their security could mean you lose trust with your audience overnight, and that’s just bad business.