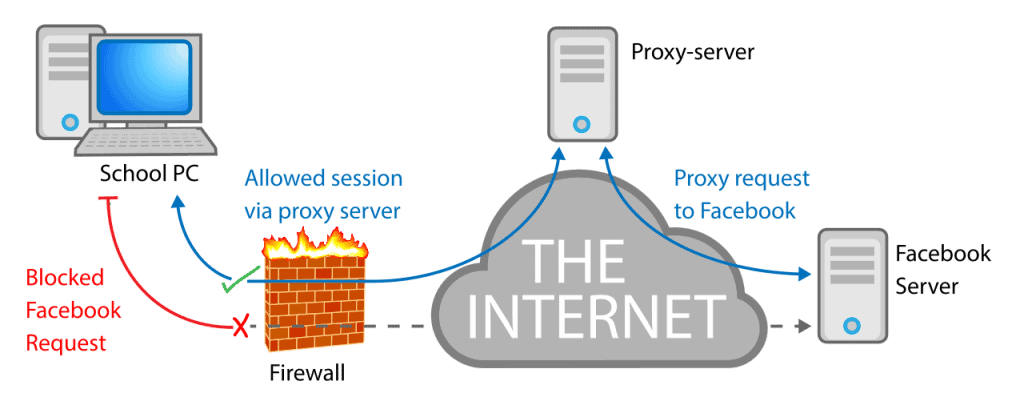
I fondly remember my days in high school, trying to find ways to beat the system instead of reading and writing my next book report in the library. It was 2005, Windows XP was all the rage, and I was fortunate enough to have learned how to employ a fair bit of rudimentary networking concepts to circumvent the school’s firewalls.
While my classmates, equally bored out of their skulls due to our latest book assignment (Wuthering Heights) tried to access their favorite forums, they found that their requests were most often denied. I had set up a proxy server at my home, and my group of nerdy friends used it to bypass the school firewalls.
While it is extremely easy to bypass school Internet restrictions, I want to be very clear on two points. First of all, I don’t advocate slacking off during learning time, despite my high school experience. And secondly, a proxy service isn’t really a great option, as we’ll discuss later.
First of all, however, we should take a closer look at how and why school campuses censor the Internet and block different types of websites.
Why Schools Restrict the Internet with Firewalls
There are many reasons why school campuses restrict their Internet connection with firewalls, but some of them may not be obvious to students at first.The most popular reason schools censor their Internet connections is to promote a greater learning experience.
This one should be a no-brainer, and by blocking distracting sites such as Facebook or Netflix, students will be less tempted to goof off when they should be studying for the next test.
But also consider that not all web restrictions are black and white. That is to say that there are other forms of restrictions (that may render a service virtually unusable) that are made for administrative purposes.
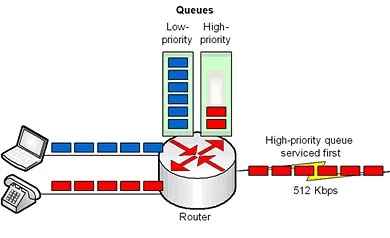
For example, consider a small middle school campus with an extremely limited budget, who can’t afford an extremely fast Internet connection. Instead of completely blocking access to a site, they may choose to place QoS controls throughout the network that help budget bandwidth for different types of services.
And this can be a huge pain. Instead of a type of web traffic (such as streaming video) being blocked completely, application traffic can be throttled to nearly debilitating levels. If, for example, a school campus decided to throttle the bandwidth of streaming video protocols, then a user might experience extremely choppy buffer rates that cause a video to take unreasonable amounts of time to load.
The good news is that this problem can be solved with VPN encryption (but not other circumvention methods such as proxy services). You see, VPN tunnels disguise the type of traffic you are downloading, making it impossible for firewalls and other network devices to see what is contained inside the encrypted payload.
As such, this will completely negate any QoS techniques that have been implemented to slow down certain types of traffic.
Methods of Circumventing Firewalls
There are two main ways to circumvent these troubling restrictions while using a school campus’s Internet connection: namely proxy servers and VPN tunnels. Let’s take a closer look at how each solution works on a more technical level, as well as the benefits and drawbacks of each solution.
First off, proxy services can be used to circumvent censorship restrictions, especially those created at the domain-level. Some campuses maintain ‘blacklists’ of website domains that they specifically block by IP address. Other campuses block DNS resolution, barring a user from obtaining the IP address of a server they want to access.
As long as DNS requests are routed through a proxy server, both of these types of restrictions can be effectively circumvented, allowing a user to access blocked websites.
However, a proxy server isn’t the most attractive option for several reasons. First of all, all of your traffic flows through the proxy server in plain text. And more often than not, if you are using a free proxy server, there’s no way of telling who maintains and manages the server.
It could be anyone, and for all we know they could be capturing traffic that flows through their server – which is illegal but happens fairly frequently.
The largest problem is that proxy servers don’t provide encryption, but this problem spawns other issues that make proxy servers a poor choice. Without encryption, using a proxy server does nothing to hide the traffic contained in the payload.
That means that your traffic is still subject to various types of QoS controls and monitoring by IT staff who will be able to see what websites you are accessing, and they even have the ability to trace the data back to your computer.
Furthermore, some campuses block certain types of proxy services. Proxy server connections aren’t integral protocols that are necessary, so some administrators choose to disable these connections completely.
So are proxy servers really a viable choice to access blocked content on a school campus? Not really, because they are rife with security problems. Sure, in the short term they may be able to unblock a website, but users who employ proxy servers are taking a lot of unnecessary risks.
Proxy Server Pros:
- Can help unblock websites
Proxy Server Cons:
- Don’t encrypt data, leaving it susceptible to interception by third parties
- You don’t always know who is running the proxy service
- Some type of proxy connections can (and often are) blocked
- Doesn’t circumvent QoS restrictions
The Preferred Solution
The best way to unlock content on a school campus is to use a VPN tunnel. VPN protocols are absolutely essential to the very core of all modern networks, and it simply isn’t feasible to block VPN connections. Doing so would leave any traffic originating from the school’s network susceptible to attacks by hackers and third parties, and cause gaping security holes that are absolutely intolerable.
In addition, VPN tunnels encrypt data, which means your data is scrambled in a manner that makes it impossible to read if it is intercepted by a third party. Every competent VPN provider is going to offer the strongest forms of security available using OpenVPN, L2TP/IPsec, and AES-256 encryption – making it impossible for even the government to read your data when it is in its encrypted format.
And because a user’s data is scrambled into an unintelligible format until it reaches the VPN server and becomes decrypted, it is incredibly easy to circumvent local network restrictions such as QoS.
That is to say that even if a school’s network administrator limits, for example, FTP traffic to 10Mbps, you will still be able to download files faster than the imposed limit since networking devices can’t see what type of traffic is contained within the VPN tunnel and administer appropriate restrictions.
Last but not least, you can always trust a reputable VPN server more than some average Joe’s proxy server. Most VPN providers don’t keep any logs of user data, and they are extremely upfront and candid about their logging policies.
Though most users feel more comfortable using a service that is located outside the US for fear of another wiretapping scandal from the NSA (such as PRISM, which harvested data from Microsoft, Google, Yahoo!, and others), most people who are just accessing video content find this data inconsequential.
VPN Pros:
- Provides encryption
- Provides anonymity by masking your IP address
- VPN providers are trustworthy and don’t keep logs
- Helps unblock websites on school campuses
- Unfeasible to block VPN connections across an entire school network
VPN Cons:
- VPN services typically aren’t free, though some providers offer free trials
Final Thoughts
To the average user, it may seem nigh on impossible to circumvent the firewall and censorship restrictions on a school campus. In reality, it’s as simple as connecting to a VPN server. Though you may be tempted to use a proxy service, I would highly advise against it unless it is a paid service – but even then, there are still security concerns if your data isn’t encrypted.
Remember, if you don’t know who is running a proxy service, you should refrain from using it. Still, these are two effective methods to circumvent network restrictions on school campuses to access web content freely.